WordPress Pete with coreruleset v3.3 out of the box and other good practices. You won’t have to worry about most hack attacks.
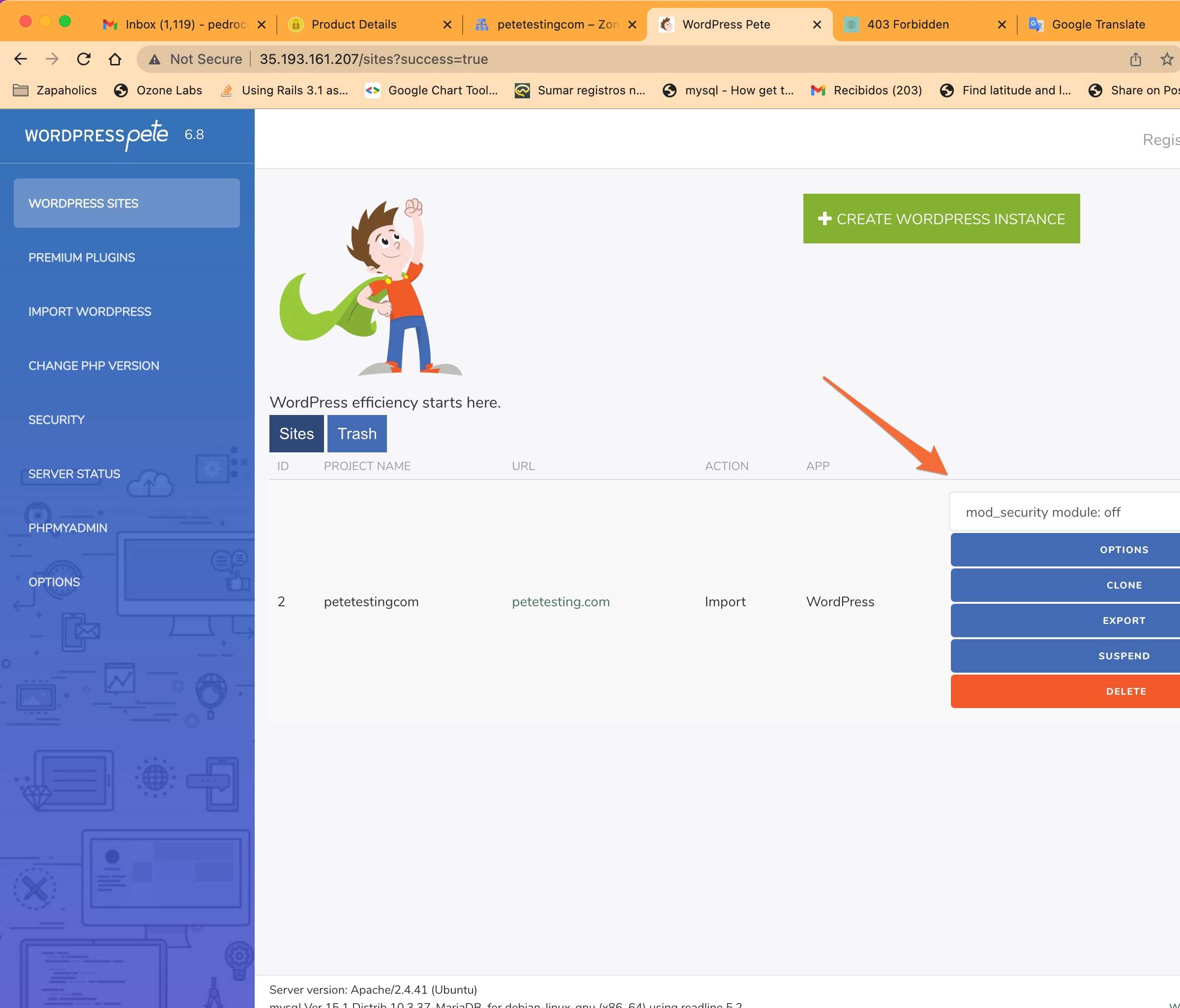
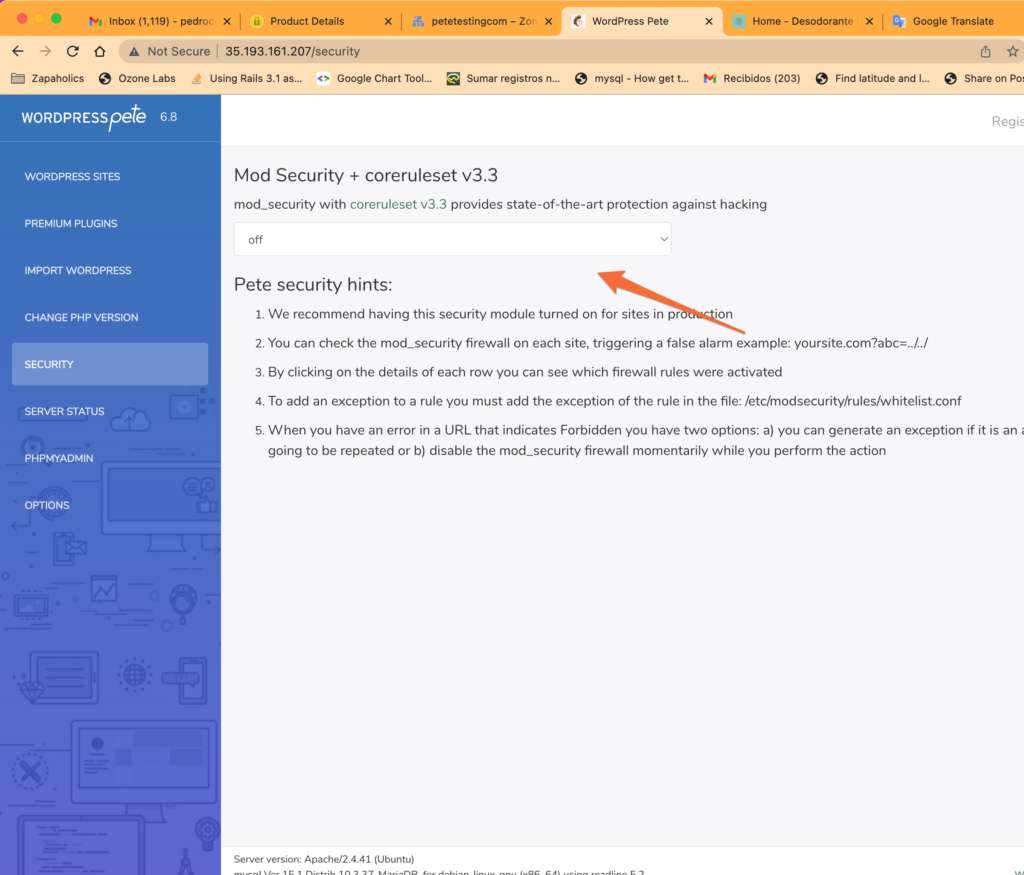
You can also disable or enable the mod_security firewall at your convenience if you are developing any feature of your site to avoid false positives. After this we recommend you activate it again
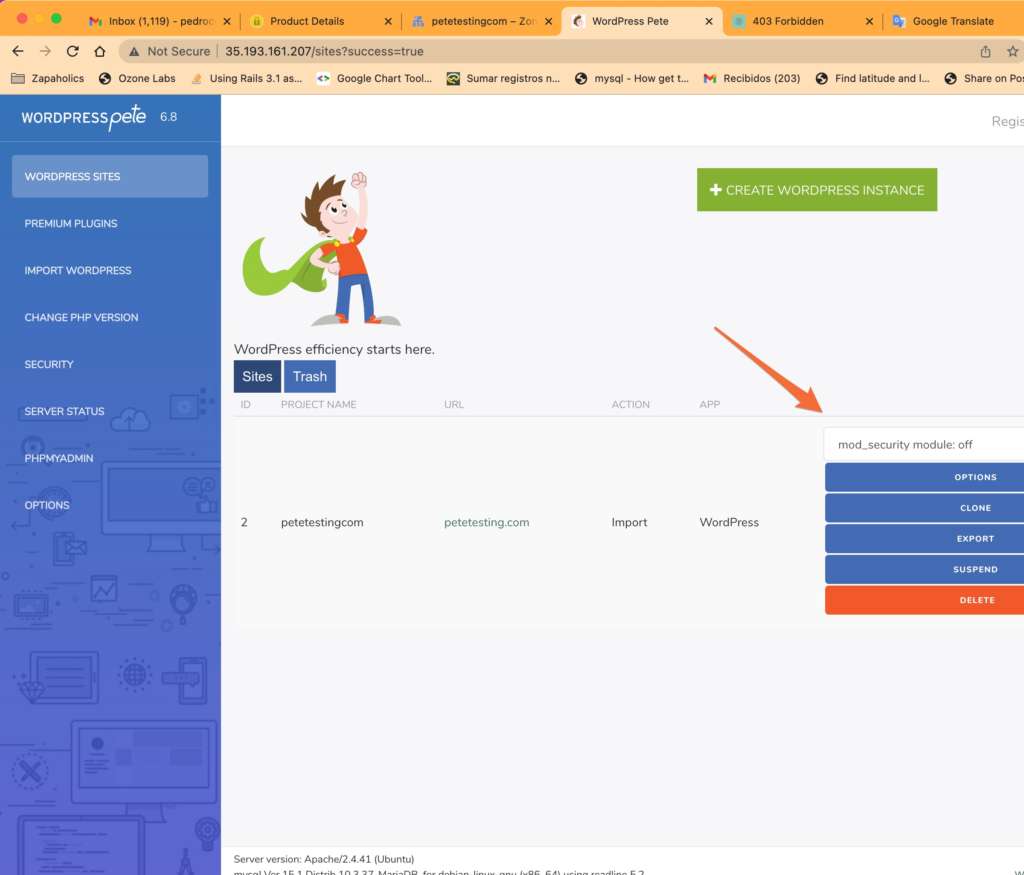
Pete also gives you the option to disable it completely or disable it per sites
You can also see in a table and easy to manage which rules were activated and the attacks that Pete’s mod_security constantly protects your site
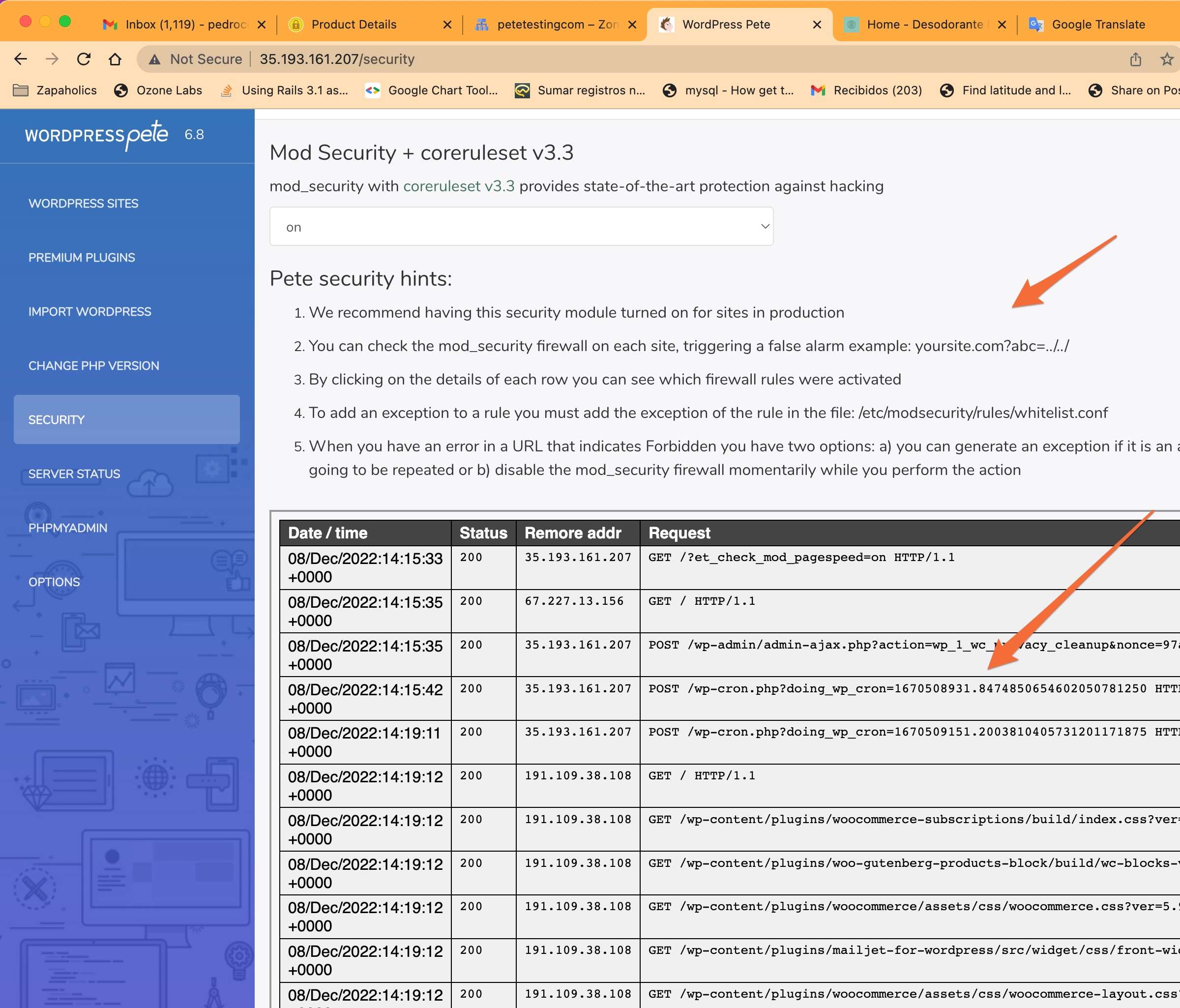
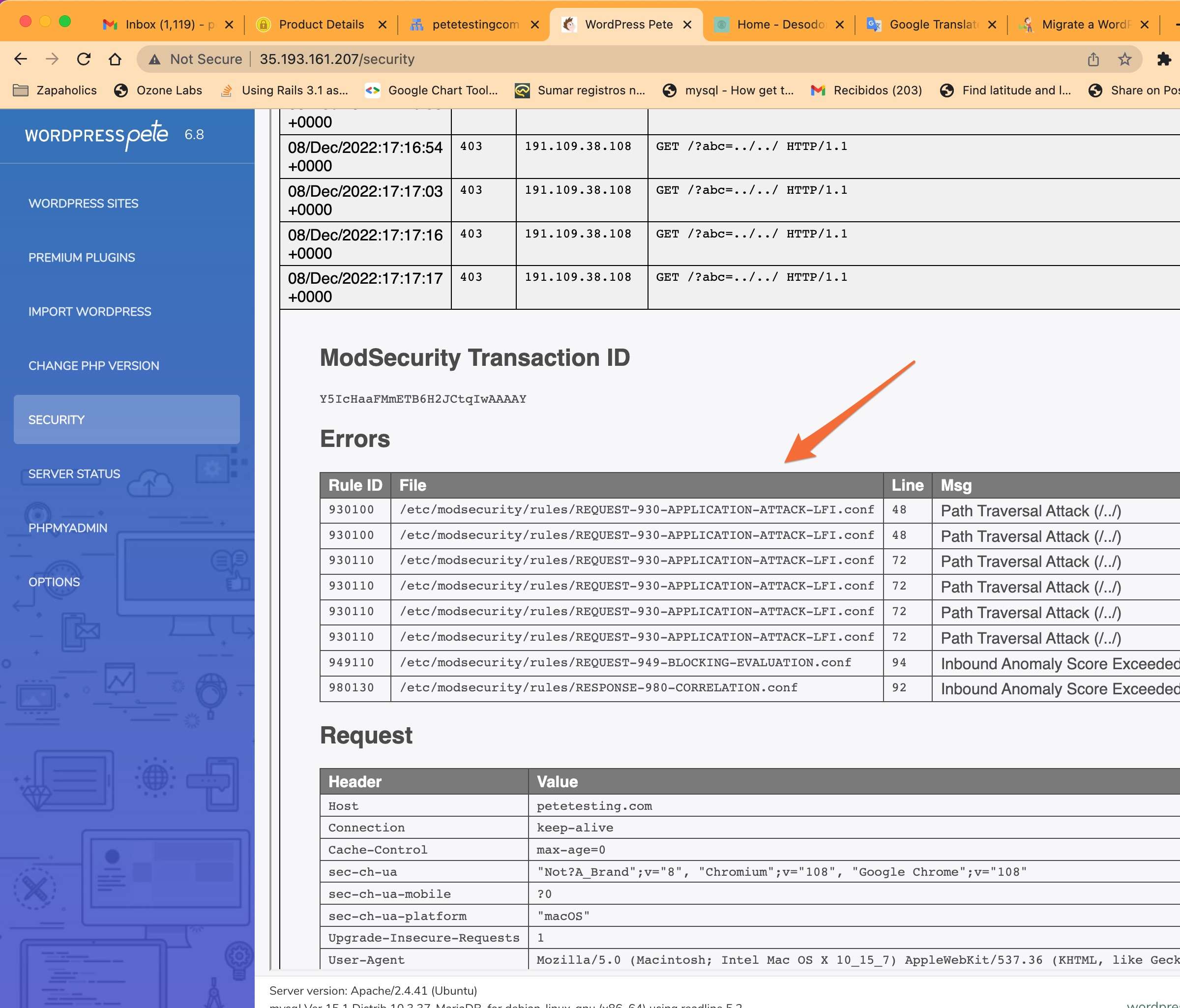
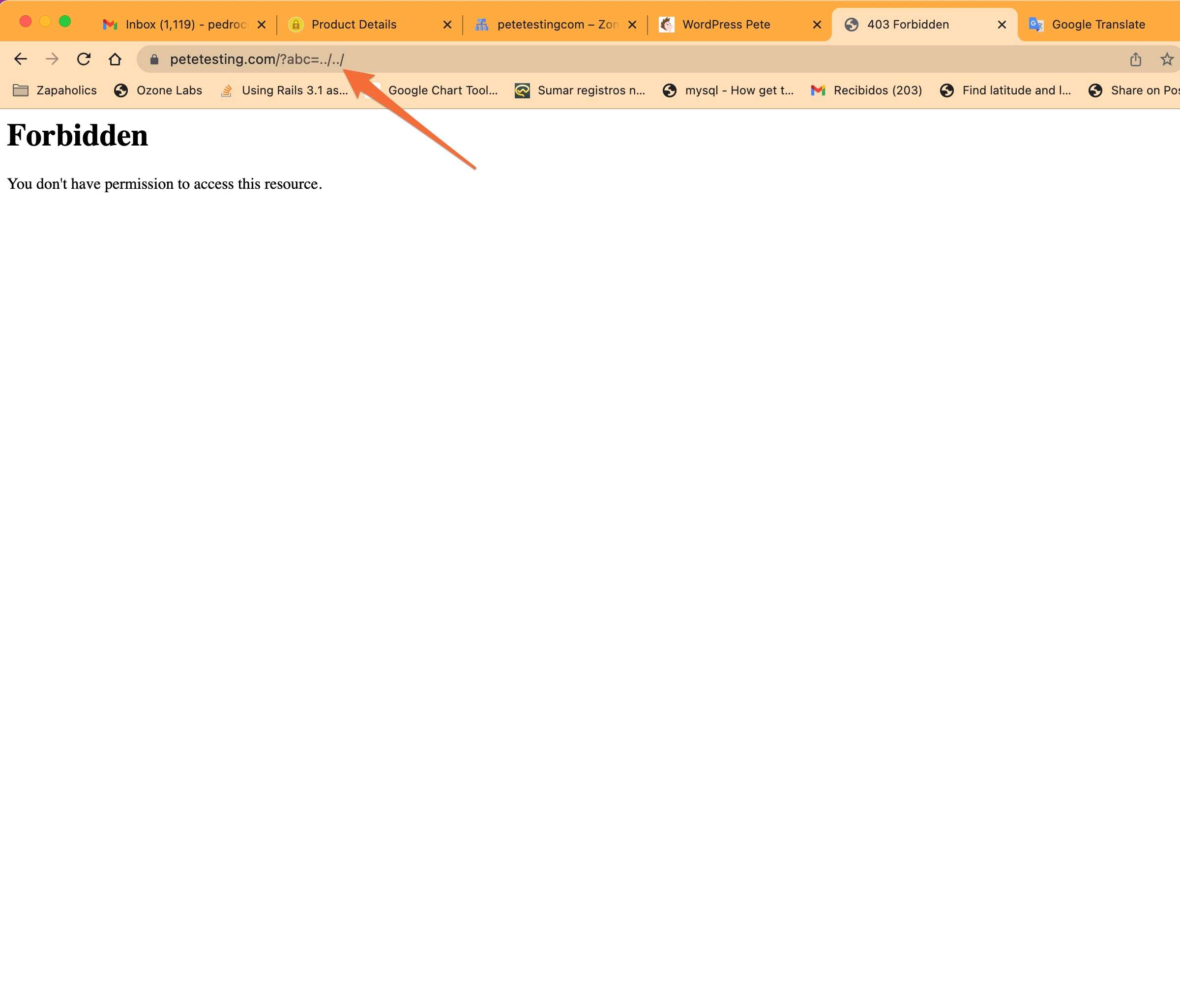
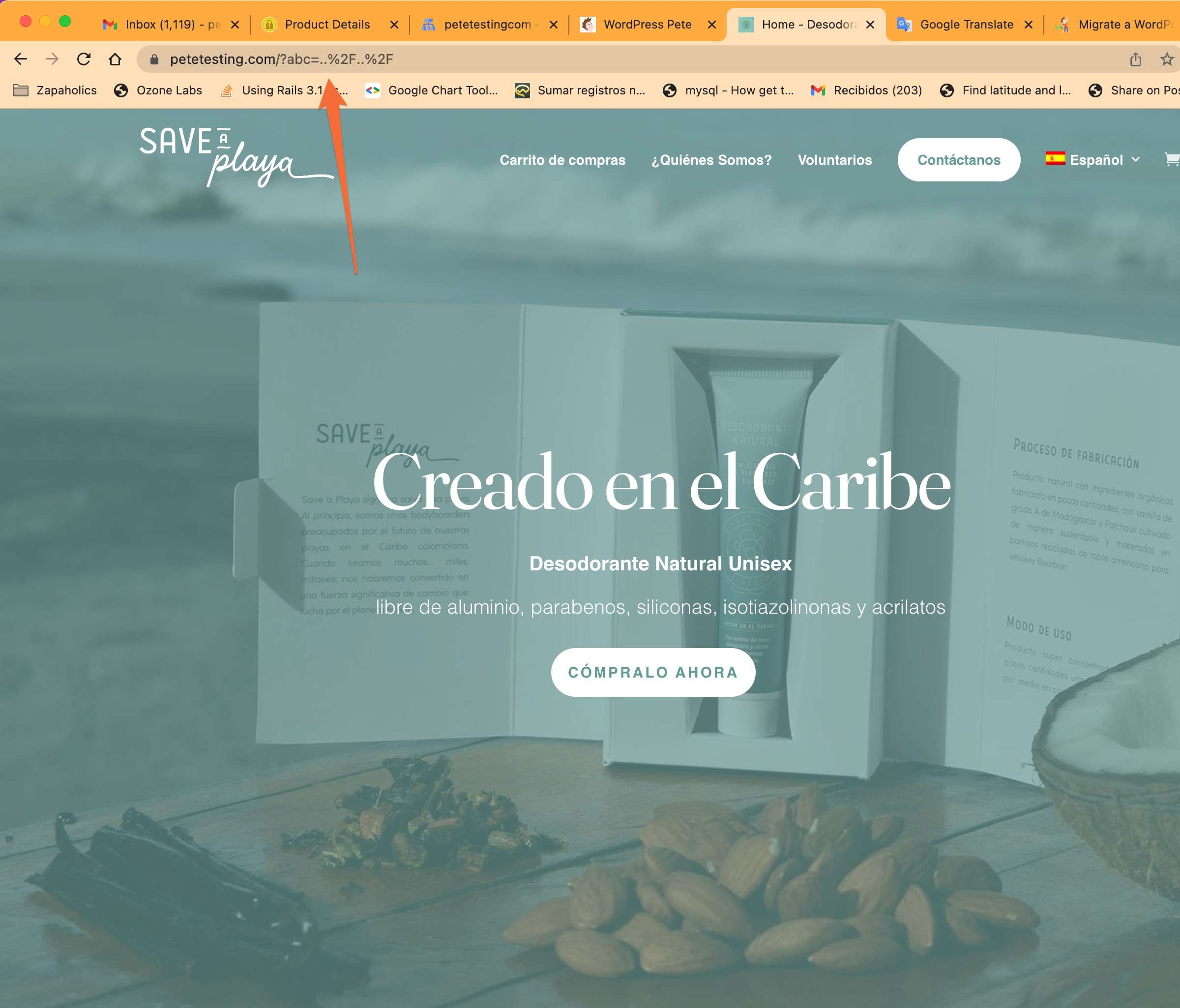
In this example you can see how we disabled the mod_security firewall and you showed the result of that address that otherwise would have triggered a protection rule